Article created by Tom Bergfeld.
Are you interested in forwarding various logs to different syslog servers?
This guide will show you step by step how to configure the product.
Please note that this guide is valid for EventReporter and MonitorWare Agent.
In our example we want to forward Windows event logs, separated by the eventlog types ‘application’ and ‘security’, to 2 different syslog servers. Of course you can also use other separators.
General information about MonitorWare Agent
General information about EventReporter
Set up an EventLog Monitor Service
At first we set up the Event Log Monitor Service. Right click on ‘Services’ – ‘Add Service’ and choose ‘Event Log Monitor’. We do not have to change anything in that configuration of our Event Log Monitor service.
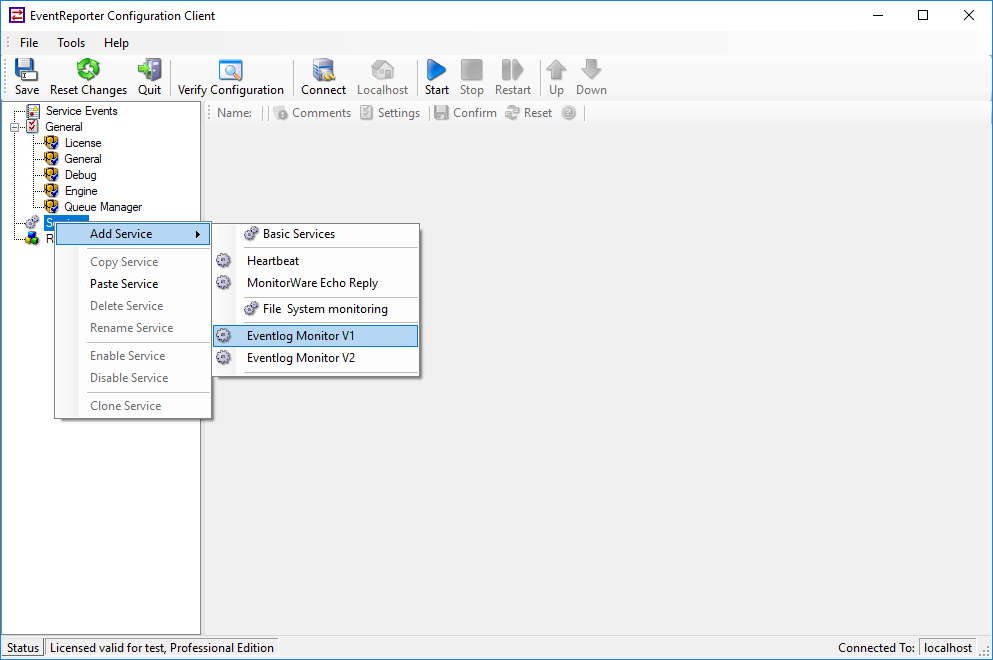
Adding an Event Log Monitor Service
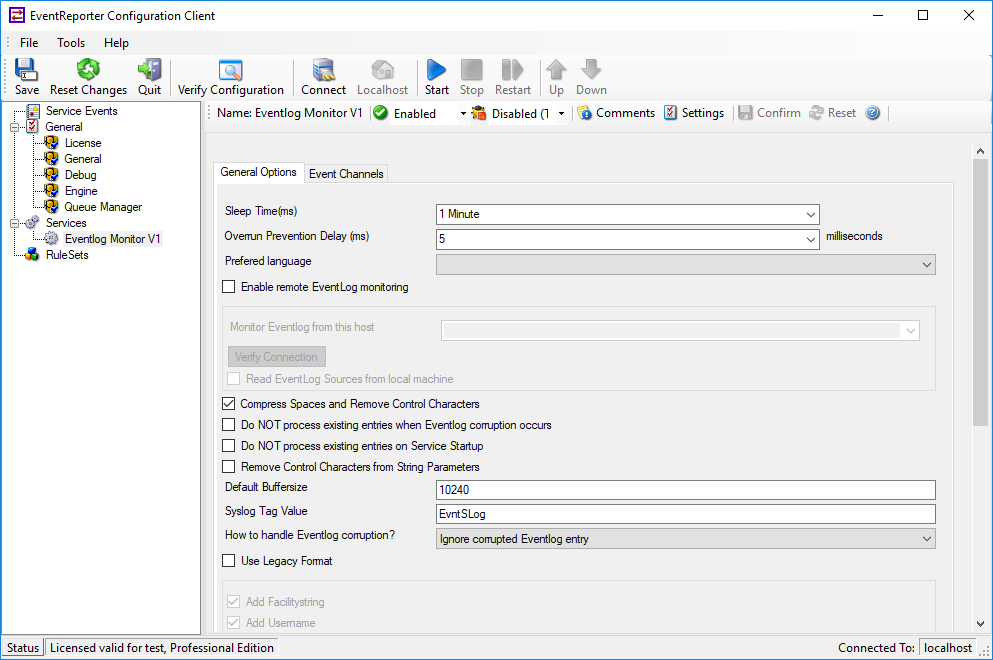
Event Log Monitor Service
2. Set up the forward via syslog action
The second step is to setup the forward via syslog actions. In our case we need 2 actions because we want to forward the logs to 2 different syslog servers. First create a Ruleset with a rule for the first forwarding action. Now we have to add a second rule for our second forwarding action.
Please note to add just a new rule – no further Rule Set. Every service can just be assigned to 1 Rule Set!
You create a new rule by right click on your Rule Set and ‘Add Rule’. Here you can add a second action like we did before. Your configuration should look like in the screenshot below.
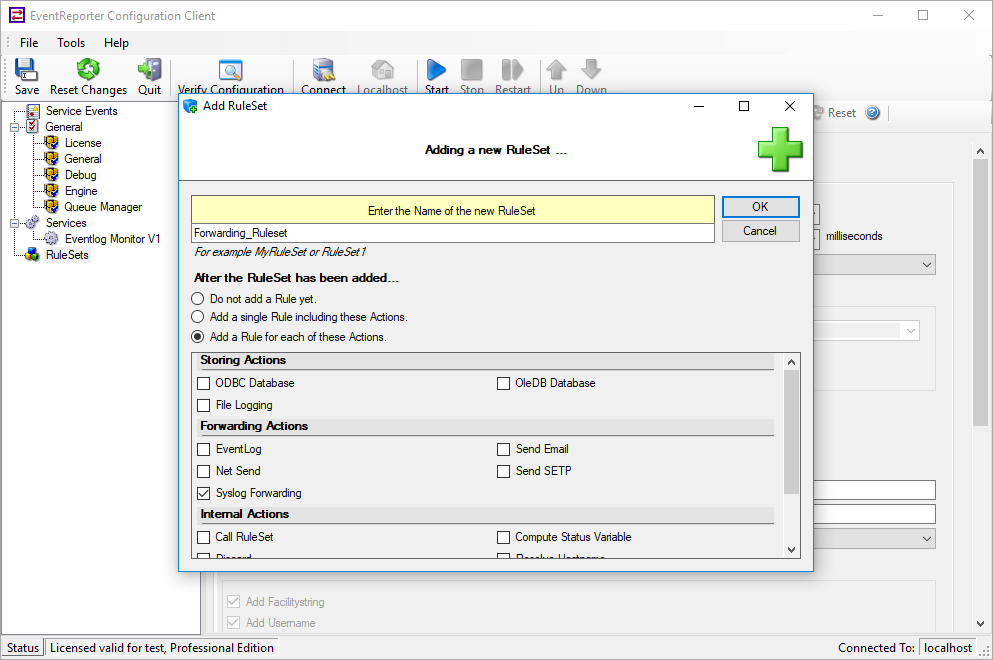
Creating Ruleset
In the added forward via syslog action we have to adjust the IPs of our syslog servers, the ports and the protocol type. The default UDP settings would be adequate for the example, but please check the firewalls of your servers if the ports are opened. The configuration of the sample configuration would look like this.
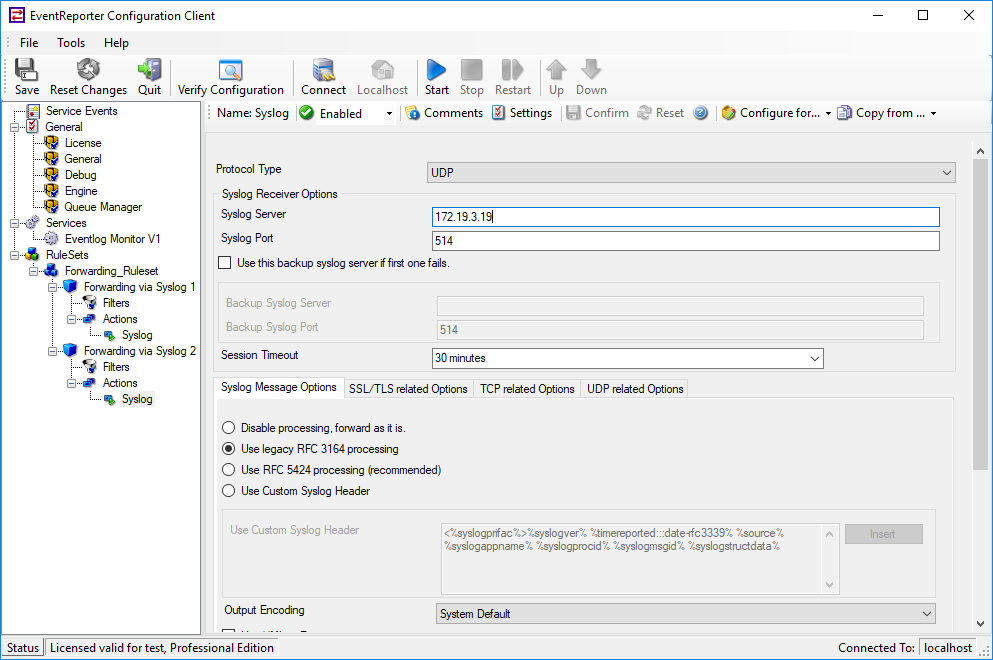
Current configuration ‘Forward via Syslog’
3. Set up the filter conditions
In this step we have to setup the filter conditions. With the filter we arrange which eventlog type will be forwarded to which syslog server. Click on your ‘filter conditions’ of your first rule. You will see that by default there is just an ‘and’ operator. Click on it and then on ‘Add Filter’and follow the screenshot to choose the ‘Event Type’ filter.
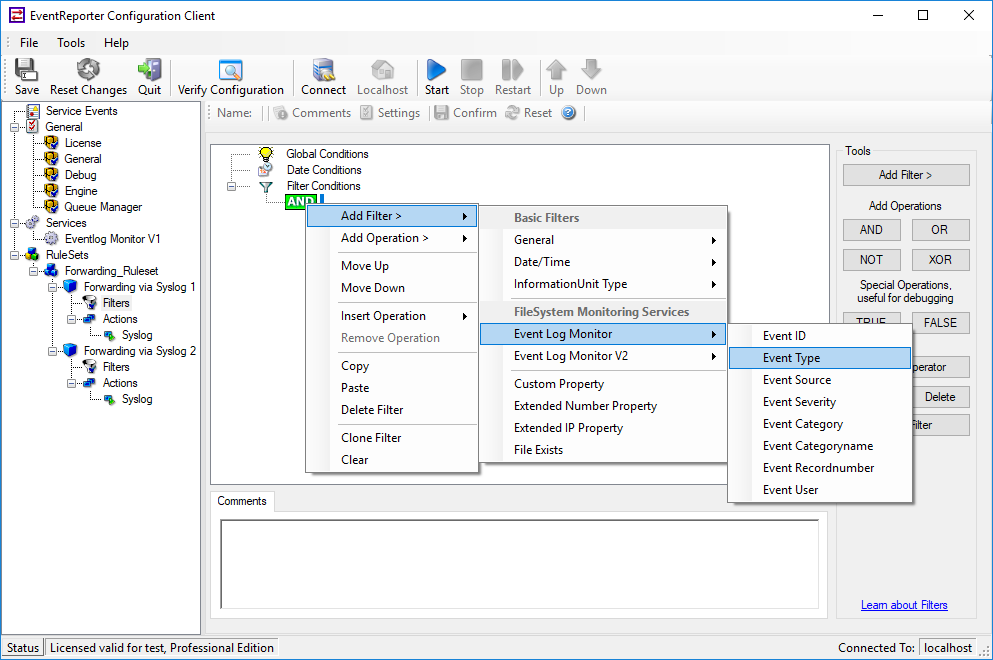
Adding the EventType filter
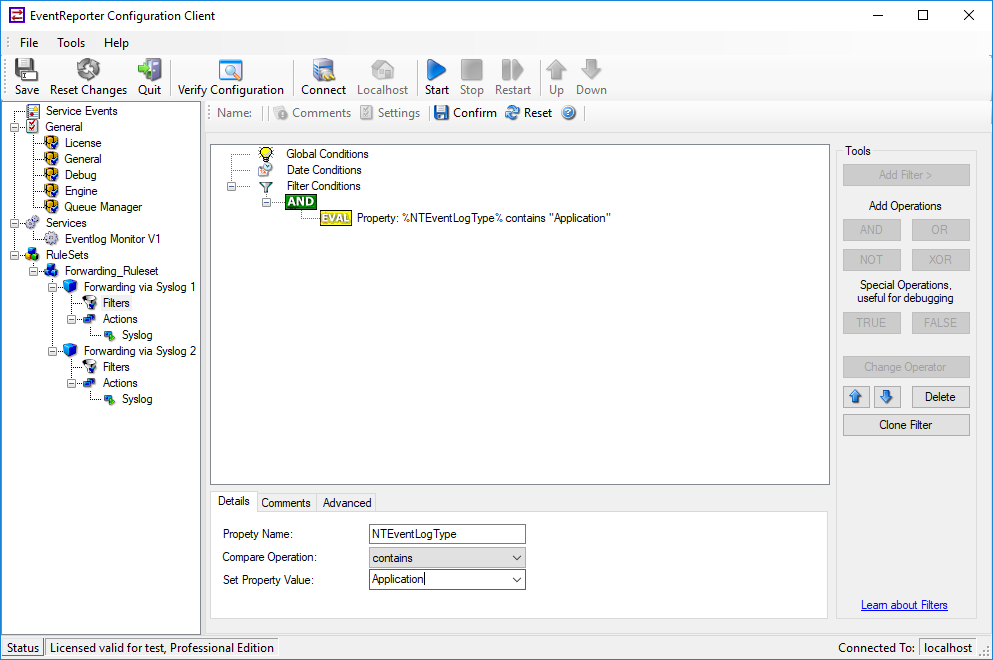
Default Event Type filter
Now we have got the first action with its filter. Repeat this step for the filter conditions of our second forward via syslog action. After adding the ‘Event Type’ filter we have to adjust the type. If we click on that filter we will see that there are some configurations for that filter. We just need the ‘set property value’ field. Here we find all types that we need. Choose the security type and save your changes.
Everything we need for this configuration is done and we can run our configuration. Just click start/restart to verify that all changes in you configuration are accepted.