Article created by Rainer Gerhards.
In this scenario, an event log monitor is used to forward all events written to the NT Event Log to a syslog server. This can either be another instance of MonitorWare or any standard syslog server, for example on a UNIX platform. The data will be forwarded in the EventReporter compatible format, as the processes running on the syslog server require that format (this is just an assumption).
This is a scenario often used together with UNIX based management solutions. The event log monitor is used here to forward events into a central repository, where it will be analyzed using pre-existing procedures.
Please note that if the data is to be forwarded to another instance of a MonitorWare Agent, we highly recommend using the SETP protocol instead of syslog – but this is beyond the scope of this scenario here.
Step 1 – Defining a Rule Set for Syslog Forwarding
The rule set specifies what action to carry out. You might be tempted to define the service first, but starting with the rule set makes things easier as it already is present when the service will be defined later and needs to be bound to a rule set.
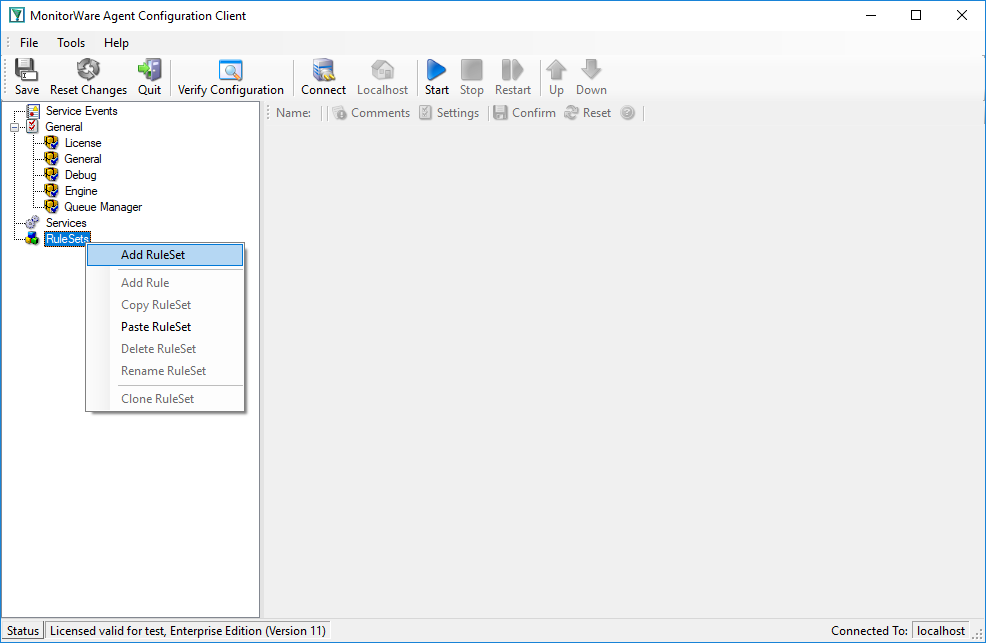
To define a new rule set, right click “RuleSets”. A pop up menu will appear. Select “Add RuleSet” from this menu. On screen, it looks as follows:
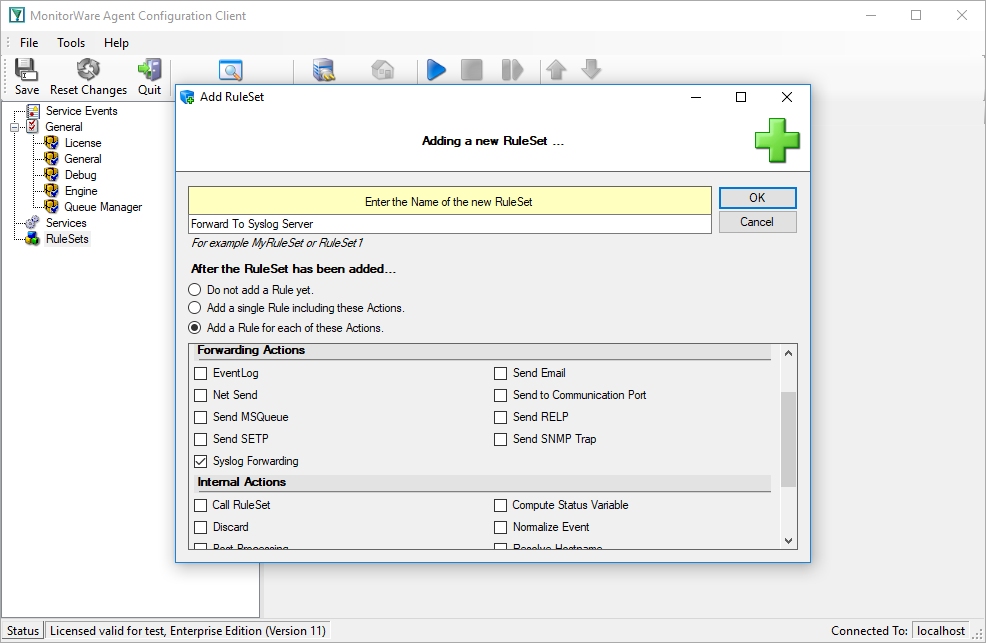
Then, a window opens. Change the name of the rule set to whatever name you like. We will use “Forward To Syslog Server” in this example. Select “Add a Rule for each of these Actions” and then the “Syslog Forwarding” action. The screen looks as follows:
Press the “OK” button and the window will close. The client shows a newly created rule set. Please expand it in the tree view until you have the following screen contents:
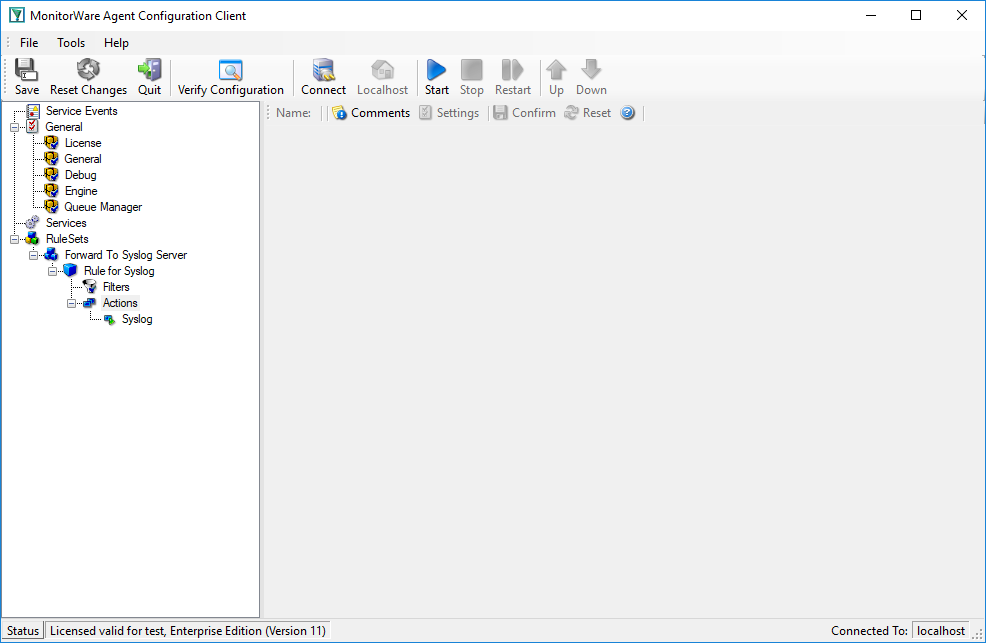
As you can see, we have a “Syslog” action configured. We will review the settings just for your information. Click on “Filters”:
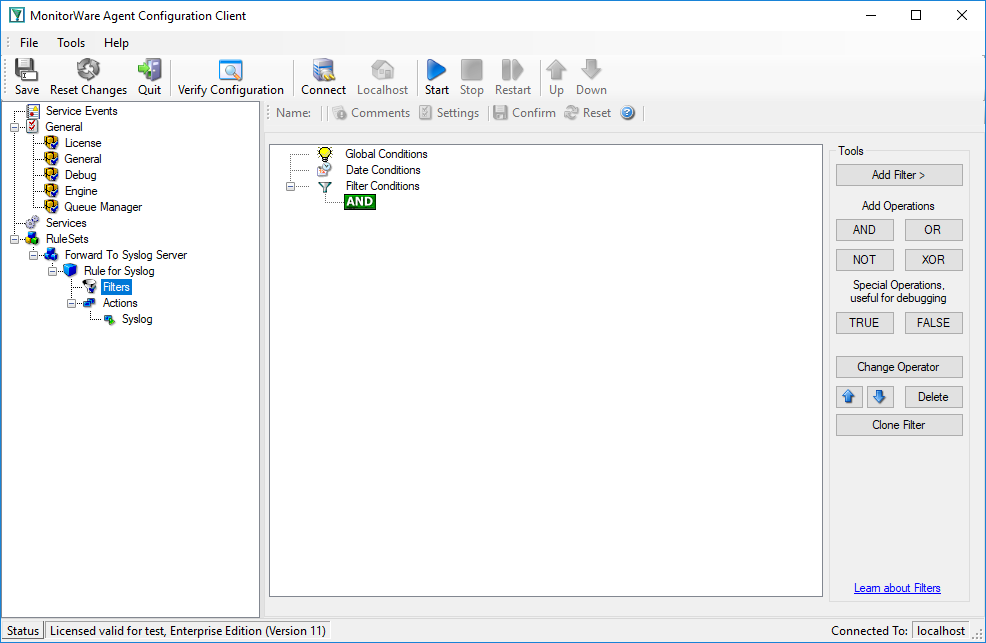
As you can see, no filter conditions are selected. This means that the all information units (the event log information) will be matched by these filter conditions. As such, the rules for the “Forward Syslog” action will always be carried out.
Now let us check the “Forward Syslog” action itself. Please select it in the tree view:
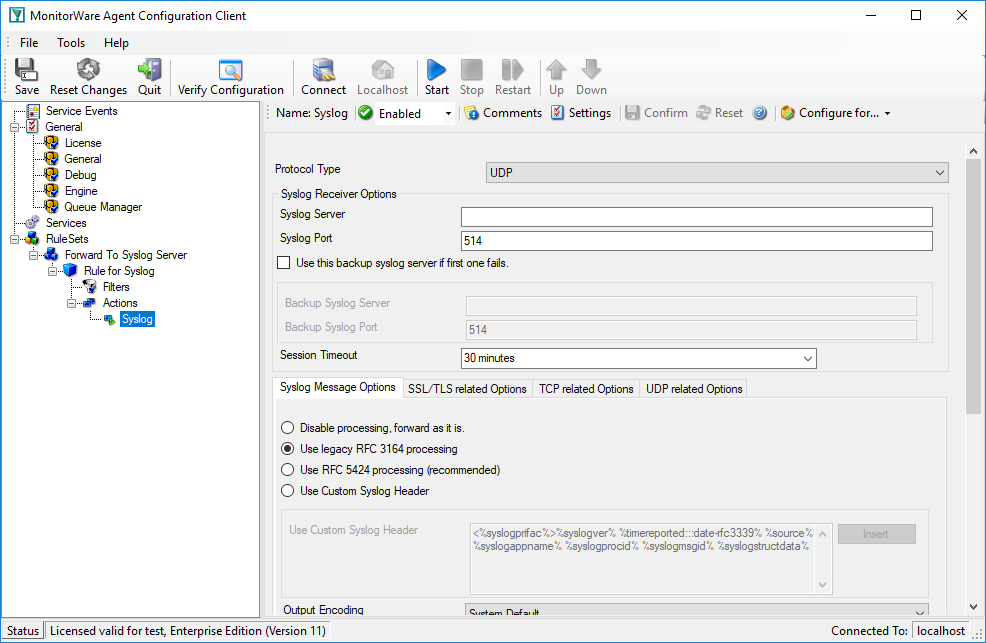
As you can see, some useful defaults are already there. It forwards syslog messages via the standard UDP protocol to the standard port of 514. These values are specified by the syslog standard and most syslog servers will expect them. Only change them if you definitely know that the syslog server is configured to use other values. If in doubt, use the default ones.
However, there are also some things that need to be completed and changed for this scenario.
Obviously, the syslog server to receive the message needs to be specified. You can use either a system name or IP address. In our sample, we will use the IP address, because this is faster and more reliable as it does not depend on DNS name resolution. Our target syslog server is on address 10.0.0.1.
After the changes, the dialog looks as follows:
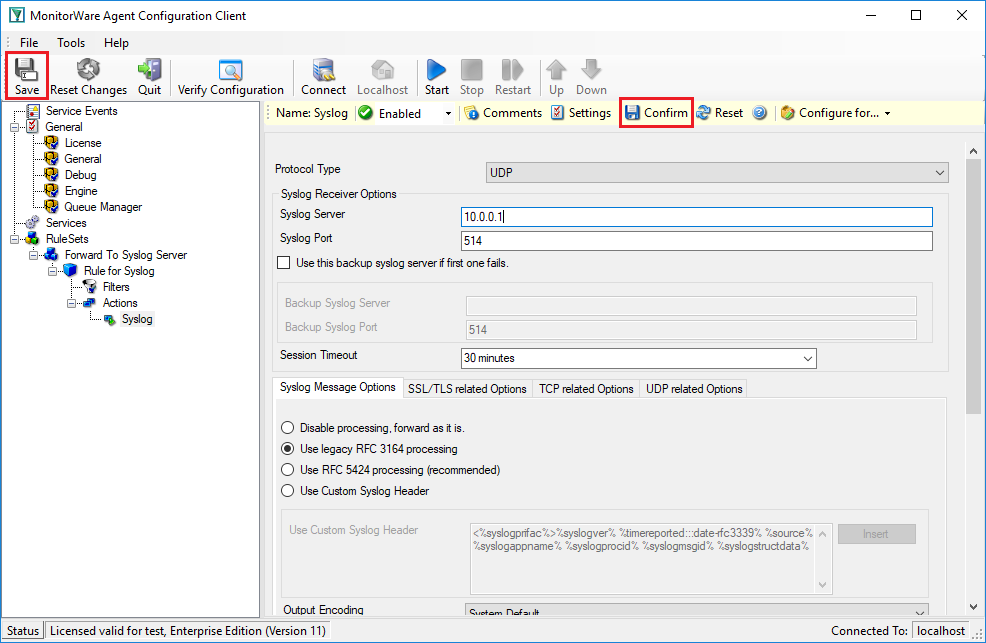
After doing so, you will notice the yellow area on top of the window. It tells you that the configuration changes have not yet been applied. To do so, press “Confirm” and then “Save”.
Now you have a workable rule set for forwarding event monitor data to the syslog server.
Step 2 – Create an Event Log Monitor Service
Now we need to define an “event log monitor” service. It is the process that monitors the Windows event log for new entries and creates information units as soon as a new entry is found. These information units are then passed to the rule set which in turn forwards them to the syslog server configured in step 1.
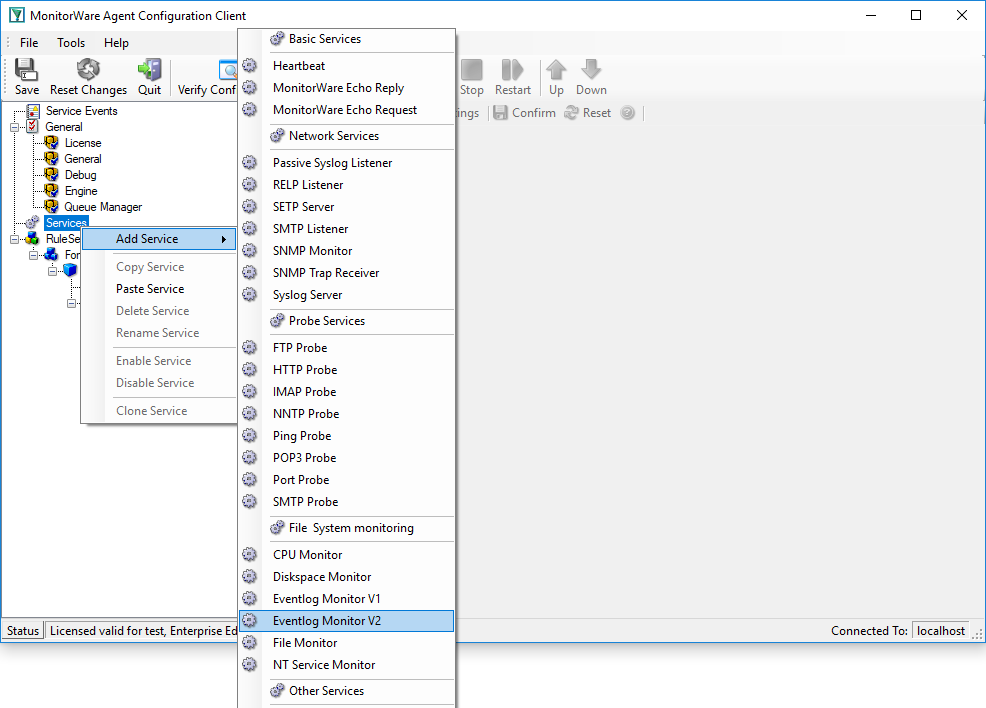
To define the event log monitor, right click on “Services”, then select “Add Service” and the “EventLog Monitor V2”:
There, you will see the newly created service beneath the “Services” part of the tree view. To check its parameters, select it:
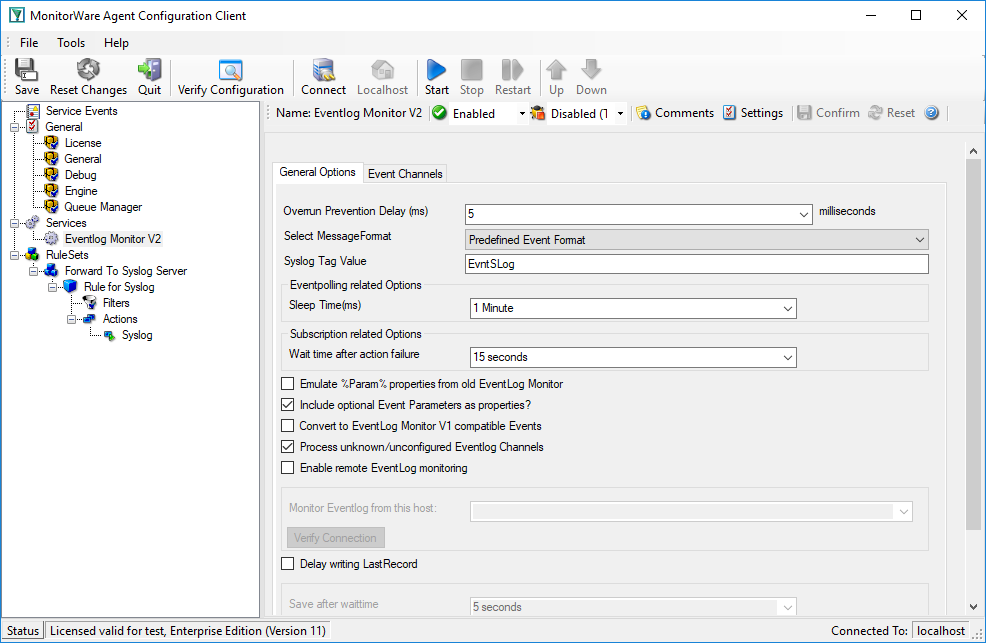
As you can see, the service has been created with the default parameters. As such, it monitors all event logs that are present on the system. It also has some protection against overruns of the receiving system or intermediary routers. It monitors the event log in a 60 second interval (sleep time of 60.000 milliseconds), which is the recommended value for typical installations.
Please note that the “Forward To Syslog Server” rule set has been automatically assigned as the rule set to use. This is the case because we already created it and it is the only rule set. By default, the wizard will always assign the first rule set visible in the tree view to new services. If that is not the intended rule set, you need to change it to the correct one here in the service definition.
Finally, we review the log specific advanced properties. To do so, click the “Event Channels” button:
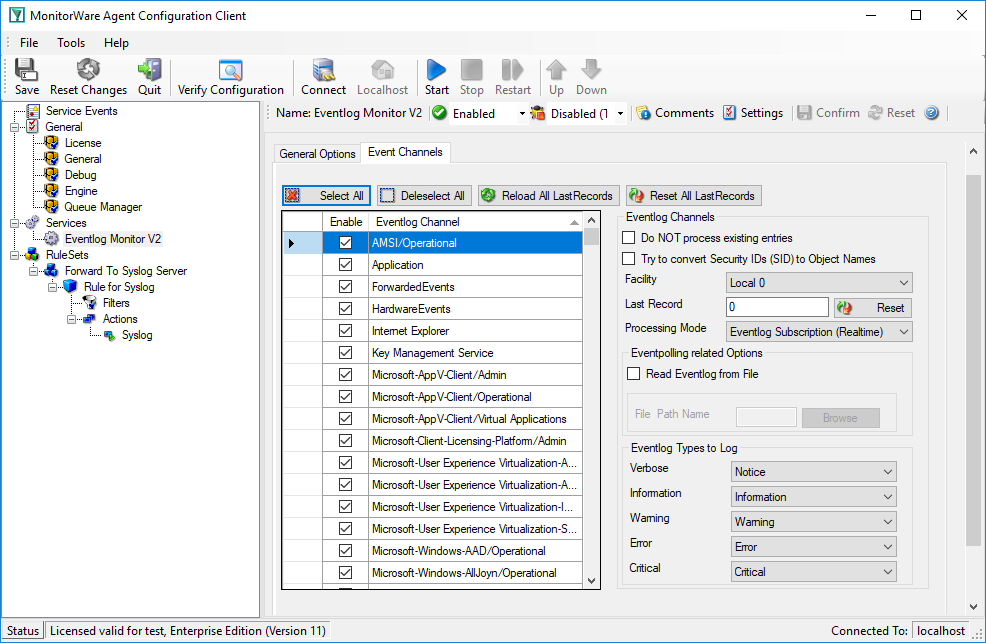
Most importantly, we can select the syslog facility that is to be used for the generated information units here. In our sample, we leave it as local.
Step 3 – (Re-)Start the MonitorWare Agent Service
MonitorWare Agent cannot dynamically read changed configurations. As such, it needs to be restarted after such changes. In our sample, the service was not yet started, so we simply need to start it. If it already runs, you need to restart it.
Service control can be done with both the respective operating system capabilities (like service manager MMC) or with the configuration client. These are shown in the red surrounded area in the following screen shot:
The buttons resemble Windows service manager – start, stop and restart. In this sample, stop and restart are grayed out because the service is not running.
After service restarts, the new definitions are active and MonitorWare Agent will forward all events from the Windows event log to the configured syslog server. Please note that on the first run, all already existing events will be forwarded. Therefore, this might take a little while. On all successive service start, only new events will be forwarded.